Our Insights
Innovative Ways - Satisfied Clientele
Innovative Ways - Satisfied Clientele
iFour Team - November 07, 2017
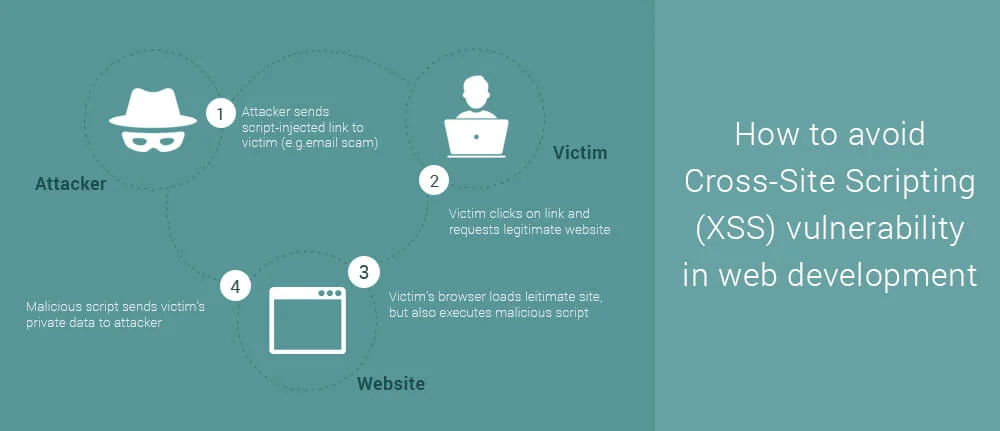
Cross-site scripting is ranked 3rd in the list of OWASP top 10 vulnerabilities 2017. Cross-site scripting are one of the most rampant occurring injection attacks faced by various web application across businesses. That’s why to know the causes of XSS, its impact and prevention is must. What is Cross-site Scripting? Cross-site scripting attacks are types of injection, in which malicious scripts are injected into trusted web applications. This attack happens when a hacker uses...

iFour Team - September 05, 2017
It has become necessary to understand the importance of security for any company including software development companies in order to provide robust, safe and secure experience to users. Actually hacking is not that much of dramatic which are shown in movies. It is dangerous enough that every business owners would be wanting to avoid it. In this blog we would try to know what is malware, how it can affect web applications and computer systems and some suggestions to protect your environment...

iFour Team - September 05, 2017
‘Insecure direct object references’ is ranked 4th on the list OWASP top 10 vulnerabilities 2013. Now days, it has become a serious concern for software development companies to maintain the privacy of all the users. This vulnerability breaches the authorization gates and allow an attacker to thieve unauthorized data from web application. Let’s have detailed understanding of this vulnerability . What is insecure direct object references? According to OWASP definition insecure...

iFour Team - August 05, 2017
Vulnerable software is threatening to our major sectors of development such as finance, defence, service industry, IT, healthcare, energy generation, manufacturing etc and many more critical infrastructures. As the digital industry is developing and becoming more and more complex, the difficulty of security increases manifolds. And therefore it is a huge risk on our parts to tolerate vulnerabilities that are exposed to risk or which are simple security problems mentioned in the OWASP Top...

iFour Team - August 04, 2017
Today’s web application is much more complex than they were in the past. These applications developed by web development companies have numerous layers due to which it increases the surface for any potential attack. During the development, deployment, ongoing use, and maintenance process of the web application, it is very important that proper security safeguards are kept by software development companies to reduce any potential ends for exploitation. We need to ensure that the security settings...