Focus on those forms and links which invoke state changing functions, because these are the most important CSRF targets.
We can user some OWASP’s CSRF testing tools to demonstrate the attack and flaws.
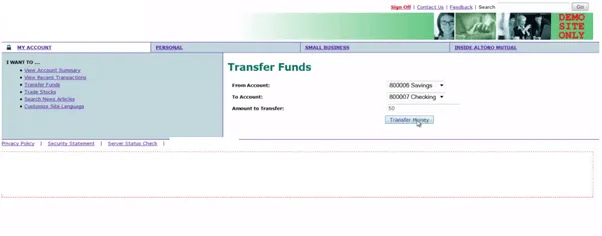
Let’s take an example to understand CSRF attack.
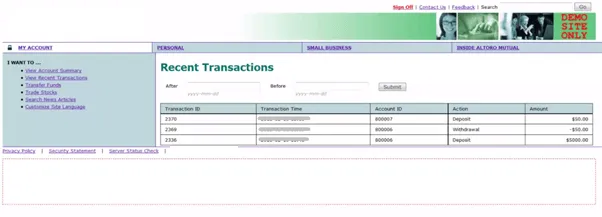
Here we have one demo website of bank. We have opened the tab to make a transaction as shown in picture.
If we transfer money (Say $50), we can it in our account history.
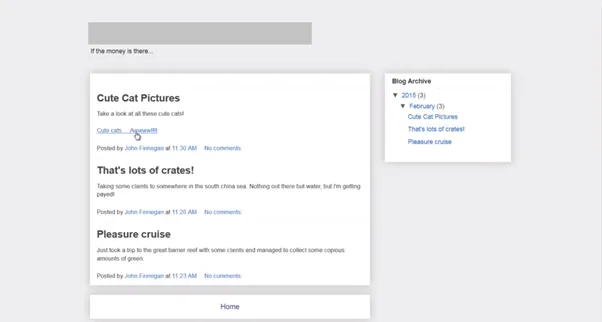
Now closing the tab and browsing something else. While browsing we see a link to see photos of cute cats.
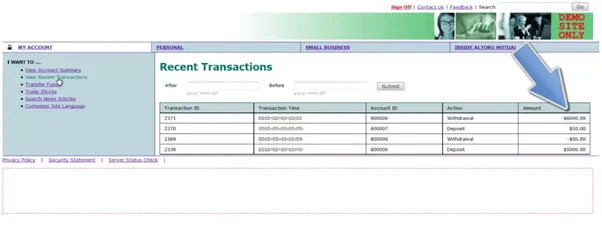
We click the link and see some pictures of cute cat. When we come back to our bank’s account we can see that $6000 has been withdrawn automatically.
It clearly indicates that clicking on any link affects another website which thieves some important data.